Introduction
Public Key Infrastructure (PKI) is a framework that enables secure communication, authentication, and data integrity through encryption and digital certificates. Organizations use PKI to manage cryptographic keys, issue digital certificates, and establish trust in online transactions. This article explores the components, benefits, and best practices of PKI.
What is PKI?
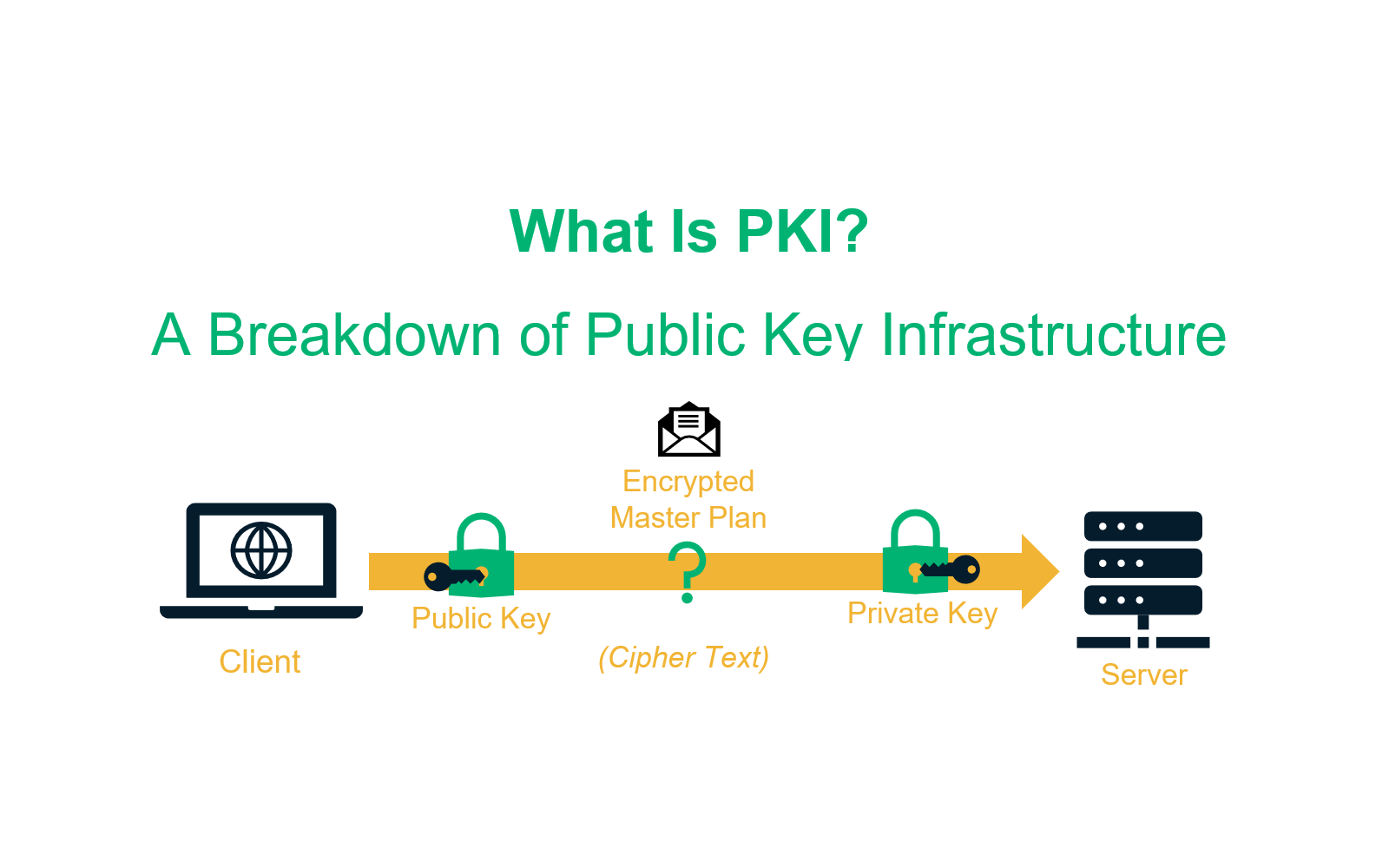
PKI is a system of policies, technologies, and procedures used to create, manage, distribute, and revoke digital certificates. It plays a crucial role in securing sensitive communications, enabling encrypted connections, and verifying digital identities.
Key Components of PKI
- Certificate Authority (CA) – A trusted entity that issues and manages digital certificates.
- Registration Authority (RA) – Verifies and approves certificate requests before forwarding them to the CA.
- Digital Certificates – Electronically signed credentials that validate the identity of an entity.
- Public and Private Keys – A pair of cryptographic keys used for encryption, decryption, and authentication.
- Certificate Revocation List (CRL) & Online Certificate Status Protocol (OCSP) – Mechanisms to revoke and check certificate validity.
- Key Management System (KMS) – Securely handles the lifecycle of cryptographic keys.
Importance of PKI
- Enhanced Security: Encrypts data and secures communications from unauthorized access.
- Authentication & Identity Verification: Ensures that entities are who they claim to be.
- Data Integrity: Prevents data tampering by verifying digital signatures.
- Regulatory Compliance: Meets security standards such as GDPR, HIPAA, PCI DSS, and ISO 27001.
- Trust in Digital Transactions: Establishes confidence in online interactions and e-commerce.
Implementing PKI
To effectively deploy PKI, organizations should:
- Define PKI Policies and Governance – Establish security guidelines for certificate issuance and usage.
- Deploy a Secure CA Infrastructure – Implement root and intermediate CAs with strong security controls.
- Automate Certificate Management – Use Certificate Lifecycle Management (CLM) tools to track, renew, and revoke certificates.
- Integrate PKI with Enterprise Systems – Secure applications, networks, and cloud environments using digital certificates.
- Monitor and Audit PKI Usage – Continuously track certificate health and compliance.
- Enable Multi-Factor Authentication (MFA) – Strengthen identity verification with PKI-based authentication.
- Secure Private Keys – Store cryptographic keys in Hardware Security Modules (HSMs) to prevent unauthorized access.
Best Practices for PKI
- Use Strong Encryption Algorithms: Implement RSA-4096, ECC, and SHA-256 for maximum security.
- Enforce Certificate Expiry and Renewal Policies: Prevent outages caused by expired certificates.
- Enable Certificate Transparency (CT) Logging: Detect fraudulent or misissued certificates.
- Implement Role-Based Access Control (RBAC): Restrict access to PKI management based on user roles.
- Regularly Audit and Test PKI Security: Identify vulnerabilities and ensure compliance with industry standards.
Conclusion
PKI is a critical component of modern cybersecurity, enabling secure communication, identity verification, and data protection. By implementing best practices and leveraging automation, organizations can strengthen their PKI infrastructure, enhance security, and maintain trust in digital interactions.